Jacob Waring – Reporter
All semester, some students have been receiving phishing emails that asked for their name, email address, password and telephone number.
Within these emails was a threat of student’s accounts being, “De- activated from the Database within the next 3 working days.”
John Jaser, director of information system, and Jeffrey Otis, director of information systems- cloud computing, both said the goal of the phishing scammer in this instance was to compromise as many accounts as possible and it seems to be proving successful.
“We average about 5 to 10 students a day, falling for scams like that,” said Jaser. “Once their account is compromised, the scammer uses a @southernct.edu account to send additional [emails].”
According to Otis, it is easier to combat scam emails when they come from external places like other counties or illegitimate domains. Yet, when it is a compromised account such as a @ southernct.edu one, it is much more challenging.
“It’s hard for us to filter that because we don’t know if that’s not legitimate as you could be sending out a questionnaire to a hundred people asking for some information because we don’t do a deep dive of the email due to privacy reasons,” said Otis.
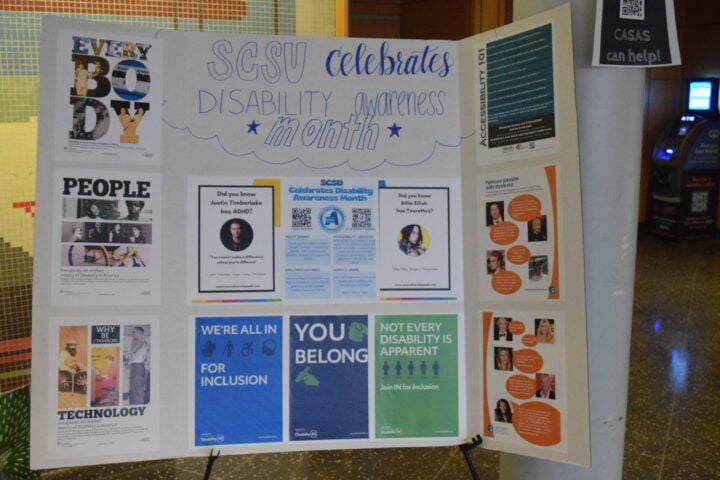
Otis said the system would start recognizing familiar patterns and prevent them from proliferating. Back in the 90’s and early 2000’s the patterns, such as misspellings, keywords and the high frequency where a “digital fingerprint,” as Jaser said, could be easily blocked.
Gmail, Outlook and other email providers, according to Otis, are cloud based and an A.I. screens through all the spam where only one percent would land in students inboxes.
Otis said the scammers know most large Internet Service Providers will not block an @edu address, and they can keep sending out emails. The A.I., in this case Outlook, will not notice until the volume of emails sends triggers to the A.I to become suspicious and spurn into action.
Luckily for students, the scammers trying to get student’s information are not using it for anything malicious beyond annoyance according to Otis and Jaser.
“The good news is what going on at Southern, is mostly trying to get students or faculty just to expose their password,” said Jaser. “And then not going after them for their bank account or steal from them, just use their account.
What we’re seeing in this case is that [scammers are] simply blasting out more emails.”
They said the best way students can combat these phishing emails is by flagging the emails which helps the A.I. respond quicker. Both Jaser and Otis confirmed the IT department is doing everything they can to prevent such scams and phishing emails, but said they will always have problems behind such emails, as scammers find new ways to subvert protections implemented.
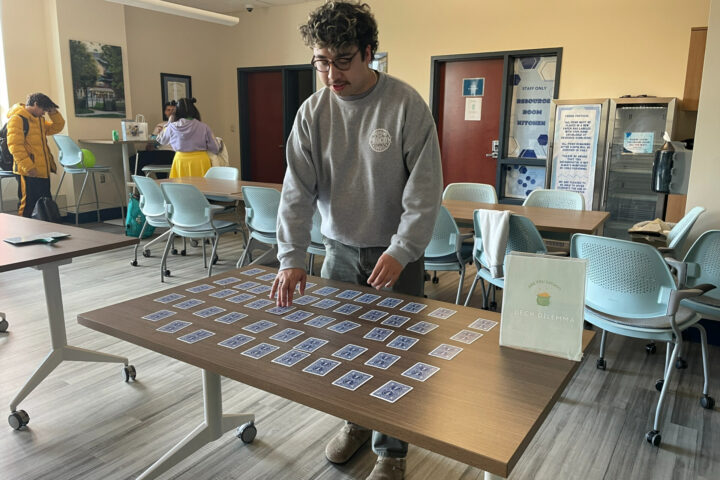
Political science major, Bret Baribault, one of the students who received a spam email, said he did not know it was a scam but erred on the side of caution. Baribault had suspicions of the phished email due to the content embedded within.
“Like, why the hell would the school want your phone, your email, and stuff like that. Like, wouldn’t they already have that?” said Baribault.
Gordon Adshade, a physics major, said he noticed the spam emails due to how they are written and the recent one going around was obvious.
“I know they’re scam emails because a lot of them have grammatical or spelling errors and the general message that they say doesn’t make sense,” he said. “The most recent one did strike me a little off guard but once I got the, ‘Hey, suspicious activity’ and I was like, ‘Alright, I didn’t do anything special,’ which made me catch on that it was a fake email.”
Photo Credit: Jacob Waring